Privacy & Data Protection by Design
As detailed in The World Model companion publication, CheshireCat® was architected from the ground up around a foundational principle: privacy is the product.
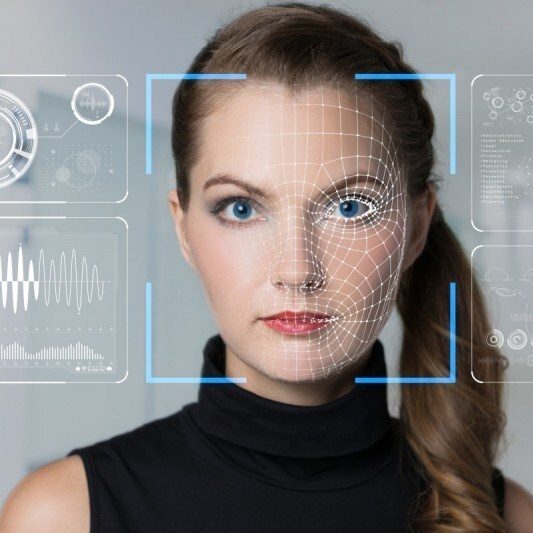
Default anonymous
Most of what a venue needs to be helpful does not require identity. Language choice, depth preference, interest vectors, comfort modes, and most operational decisions can all be made from environmental state — without knowing who anyone is. CheshireCat® defaults to anonymous mode: it can count, route, and serve visitors without ever storing an identifying image.
Local processing, no cloud dependency
All recognition processing happens locally on standard compute nodes — no cloud connection required, no data leaves the venue. This eliminates the attack surface of centralized databases and ensures compliance with data sovereignty requirements across jurisdictions. With ~0.5 second response times and fully isolated operation, CheshireCat® provides recognition capabilities that meet the most stringent security requirements.
Consent-first architecture
For venues that offer personalized experiences, CheshireCat® operates on explicit opt-in only. Visitors who choose personalization receive it. Visitors who don't are respected — and still benefit from anonymous crowd flow optimization and content pacing. "Redacted occlusion" lets venues count and route anonymous visitors without ever retaining an identifying image.
Minimization and forgetting
The system is designed to minimize what a venue knows while maximizing what a visitor gets. Session data is short-lived and purpose-specific. When something must be retained, it is retained for a specific purpose, for a specific time, with a deletion posture that is part of the system's rhythm. As the publication states: "Forgetting is what makes systems safe in public space."
Compliance across jurisdictions
Because CheshireCat® processes locally, stores minimally, operates on consent, and deletes by design, it supports compliance with privacy frameworks worldwide — including GDPR's data minimization and purpose limitation principles, CCPA's consumer rights provisions, biometric information protection requirements, and sector-specific regulations governing visitor data in public spaces. The architecture ensures that operators can deploy recognition capabilities in any jurisdiction with confidence.